Summary
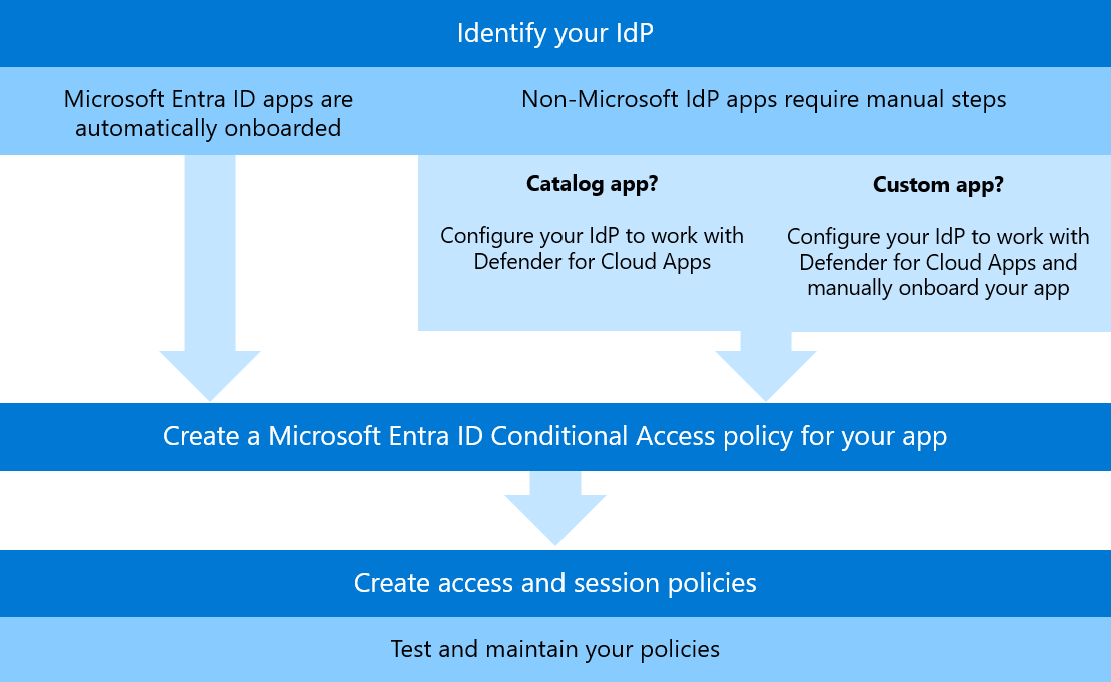
An often overlooked control that your organization may already pay for, but underutilize, is Defender for Cloud Apps + Conditional Access policies. These are surprisingly effective, straightforward to set up, and granular once you get a handle on the process. In my cloud apps hardening journey, I found that this specific use case (and many more!) are not well documented or laid out as clear as they could be in Microsoft documentation. Instead of paying a third-party for their bespoke product, you can leverage the capabilities of MDCA and conditional access to act as a reverse proxy for your Entra ID user authentication traffic.